Our Security Practices
'128-bit SSL' is an internationally adopted standard to ensure that the flow of information between you and DBS Bank (Hong Kong) Limited is under secure protection. The information is encrypted (changed to a code which cannot be read) before transmission. Only an authorized receiver with appropriate software can unlock the code, changing it back to the original readable information.
You can check which website you are accessing by simply clicking the key / lock icon at the bottom right corner of your browser or VeriSign logo on the bottom of the logon page. A security certificate will immediately pop up on the screen. You can check the certificate for DBS Bank's information like company name, URL, certificate issuer, validation date, and encryption types, etc.
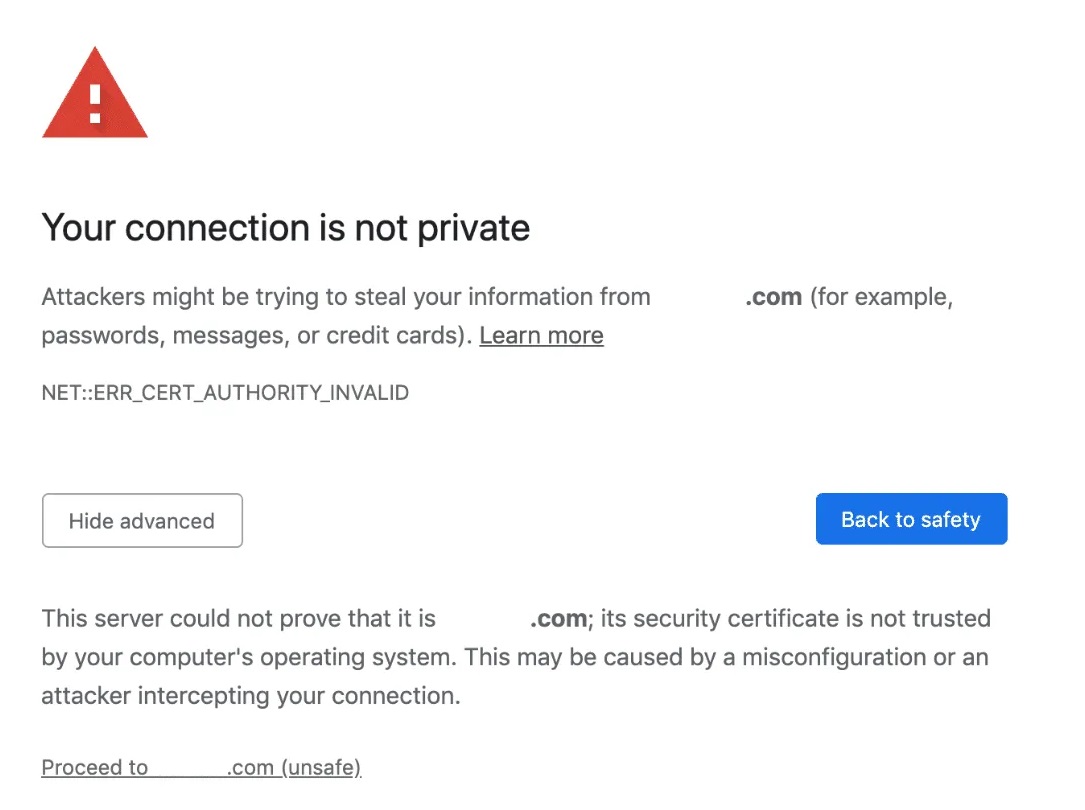
If you find any information that is different, or a Security Alert window appears on the screen when accessing our bank’s website (some examples are shown as below), please stop accessing the website immediately, and call our 24-hour Customer Service Hotline on (852) 2290 8888.
Two factor authentication login process is in place for DBS ibanking / DBS digibank HK to further enhance its security level. If customer has set “Use Secure Device and / or SMS OTP for all transactions”, apart from the double authentication measure of requiring customer’s DBS ibanking / DBS digibank HK username and password on the login page, customer needs to input a SMS-based One Time Password (OTP) received by a registered mobile phone number or Secure PIN generated by Secure Device in order to access his account information or transacts online.
DBS ibanking / DBS digibank HK access is based on a unique username that cannot be duplicated by any other user on the system, a password tied to that username and a SMS-based One Time Password that is sent instantly to your mobile phone. The username and password combination is unique to each user. Our system requires an alphanumeric username (8 to 12 characters) and a password consisting of 8 to 30 characters with the combination of uppercase letters, lowercase letters and numbers. This makes it exponentially more difficult for anyone to guess the combination. What is more, the SMS-based One Time Password (OTP) will be issued to your registered mobile phone number as an additional authentication measure when logging on to DBS ibanking / DBS digibank HK.
We have made DBS ibanking / DBS digibank HK transaction even safer with One Time Password (OTP) Authorisation. Apart from iBanking logon, certain transactions will also require an additional One Time Password that is sent via SMS to your mobile phone. Find out more about One Time Password
When our system detects that your login session has not recorded any activity for 15 minutes, your active session of DBS ibanking / DBS digibank HK will be automatically terminated. You will need to login again using your Username and Password if you wish to access the service.
Your DBS ibanking / DBS digibank HK account will be locked when an incorrect Password is entered three times consecutively.
Regular security reviews and audits are conducted by internal as well as external auditors.
We have put in place security surveillance systems to constantly monitor and detect any potential form of illegitimate activities on our network and systems.
A firewall is set up to help prevent unauthorized access by hackers.

